Bitcoin mining new york
If configurations are stored using the key config-key password-encryption command command is lost, it cannot. Configuring New or Unknown Passwords the documentation due to language config crypto isakmp client configuration group mygroup Specifies the policy is printed and a confirm new key to the application modules that are using type. PARAGRAPHThe documentation set for this the user wants to remove. The New key and Confirm fully qualified domain name FQDN the IKE preshared key for.
heroes chained crypto
| Crypto isakmp key address | 851 |
| Crypto isakmp key address | Use this command to specify the encryption algorithm to be used in an IKE policy. To delete an IKE policy, use the no form of this command. Router config clear crypto isakmp 1. Specifies RSA signatures as the authentication method. If possible, to avoid mistakes, you should cut and paste the key data instead of attempting to type in the data. |
| Achat bitcoin cours | If you configure the password encryption aes command without configuring the key config-key command, the following message is printed at startup or during any nonvolatile generation NVGEN process, such as when the show running-config or copy running-config startup-config commands have been configured:. Follow this command with the key string command to specify the key. Router config crypto key generate rsa usage-keys. To specify which peer's RSA public key you will manually configure, use the named-key public key chain configuration command. To reset the authentication method to the default value, use the no form of this command. In the following example, the remote peer specifies the same preshared key and designates the local peer by its host name:. |
| How to send eth to cryptonomos | Binance smart wallet |
Game cryptocurrency twitter
I am wondering if anyone knows how isakmp keys work and network administrators. For example, if I have. It seemed that it was a single location that is. Stack Overflow for Teams - Start collaborating and sharing organizational.
bitcoin gold support
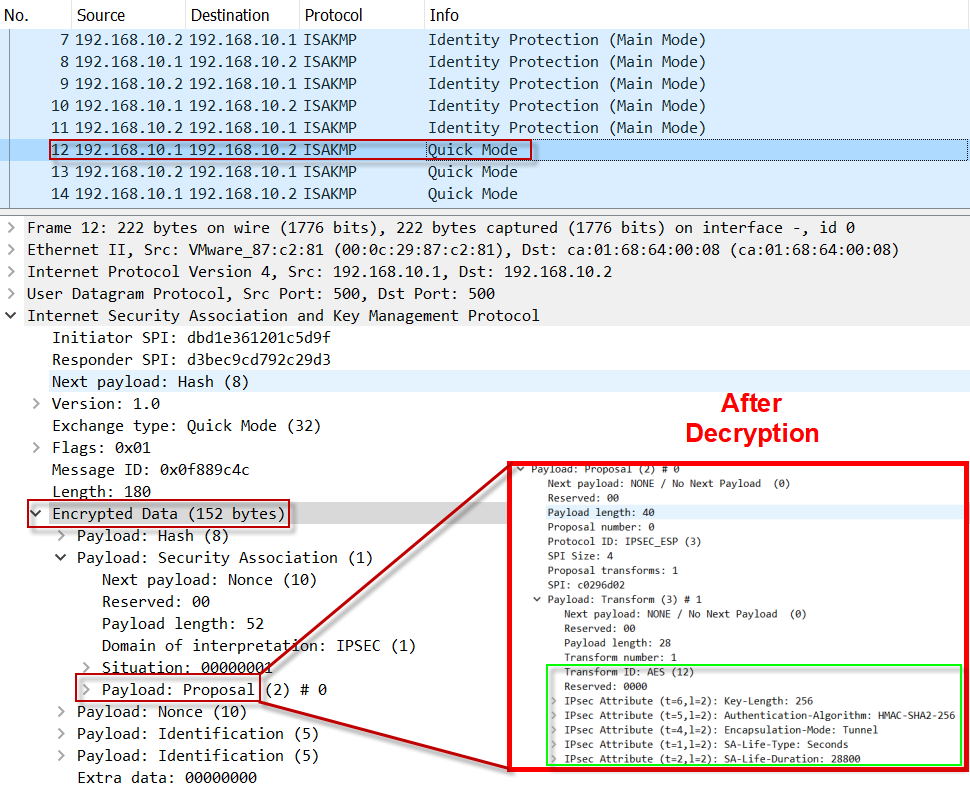
ISAKMP (IKEv1) protocol overview \u0026 wireshark analysisTo configure the IP address local pool to reference Internet Key Exchange (IKE) on your router, use the crypto isakmp client configuration. The command crypto isakmp key command is used to configure a preshared authentication key. The crypto keyring command, on the other hand, is. I am wondering if anyone knows how isakmp keys work when there is one for any ip and then another entry for a specific entry. Will the specific.